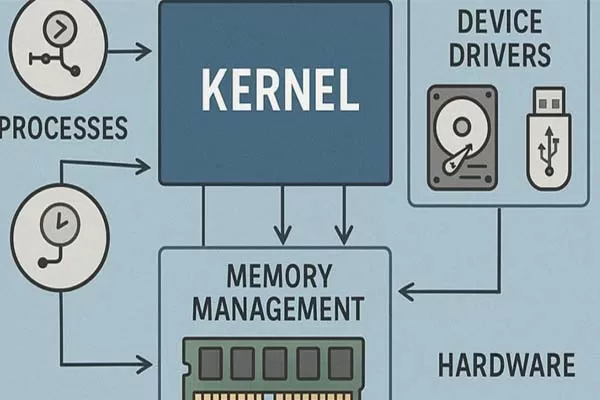
The kernel is the core part of an operating system (like Linux kernel or Windows NT kernel).
- Memory
- CPU processes
- Hardware communication
- System security
Because it runs with the highest privileges, any bug in the kernel is extremely dangerous.
A bug is a flaw or mistake in code. These bugs can be:
- Accidental (coding errors)
- Intentional (malicious vulnerabilities exploited by attackers)
1. Buffer Overflow Attacks
- Occur when a program writes more data than memory can hold
- Overwrites critical kernel memory
- Attackers inject malicious code
Result: Full system control
2. Privilege Escalation
- Normal users exploit bugs to gain root/admin access
- Often caused by improper permission checks
Example: A simple app becomes a gateway to system-level control
3. Race Conditions
- Two processes access shared resources at the same time
- Kernel fails to handle timing correctly
Attackers manipulate timing to bypass security checks
4. Null Pointer Dereference
- Kernel tries to access memory that doesn’t exist
- Can crash the system or be exploited
Result: System crash or exploit entry point
5. Use-After-Free Vulnerabilities
- Kernel uses memory after it has been freed
- Attackers replace that memory with malicious data
Result: Execution of attacker-controlled code
6. Integer Overflow
- Mathematical operations exceed allowed limits
- Leads to incorrect memory allocation
Result: Memory corruption
7. Device Driver Exploits
- Drivers run in kernel space
- Poorly written drivers introduce vulnerabilities
Example: Faulty GPU or network driver compromising the system
Real-World Examples
- Dirty COW
→ Allowed attackers to gain root access - BlueKeep
→ Remote kernel-level attack via RDP
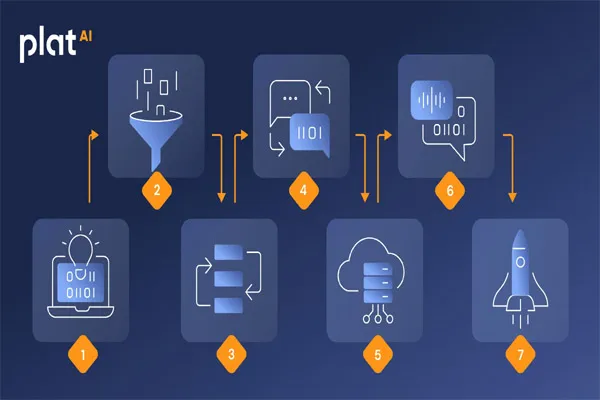
How Attackers Use These Bugs
- Find vulnerability in kernel code
- Create exploit (malicious program)
- Trigger the bug
- Gain control over system
- Install malware or steal data
Protection Mechanisms
Modern kernels use strong defenses:
- Address Space Layout Randomization (ASLR)
- Kernel Patch Protection
- Secure Boot
- Memory protection (DEP)
- Regular updates and patches